
As DeFi evolves toward real-world asset (RWA) integration, protocols are increasingly becoming hybrid systems- where critical data elements originate off-chain and are pushed on-chain.
This includes:
Asset valuations (AUM / NAV)
Oracle price feeds
Settlement approvals
Automated service wallet actions
While this unlocks powerful use cases, it also introduces a new and often underestimated risk: Off-chain inputs can become the weakest link in an otherwise secure system.
When Smart Contracts Work, But Systems Fail
A recent exploit on a crypto protocol occurred due to systems failing, although the smart contracts functioned exactly as designed. The root cause was not a bug in the smart contract logic.
Instead, the system relied on an off-chain service with a privileged key to approve minting. Once that key was compromised, the attacker could authorize arbitrary mint txns because:
There was no on-chain upper bound
No validation of mint-to-collateral ratio
No safeguards against abnormal values
The system trusted the input, and it caused the exploit.
The Hidden Risk: Service Wallets & Oracle Roles
In many DeFi protocols, certain roles are assigned to service wallets, often backed by infrastructure like AWS KMS.
These roles typically:
Update AUM or NAV values
Push oracle data
Trigger automated protocol functions
In cSigma, this responsibility is explicitly defined through:
ROLE_ORACLE_MANAGER
This role exists because RWA systems require off-chain asset reporting. However, assigning such a role introduces a fundamental question:
What happens if that wallet is compromised?
Most systems assume:
“The wallet is secure”
“Infrastructure is reliable”
But secure design requires assuming the opposite instead.
What if it fails?
Naive Design vs Defensive Design
A naive implementation of AUM updates would look like this:
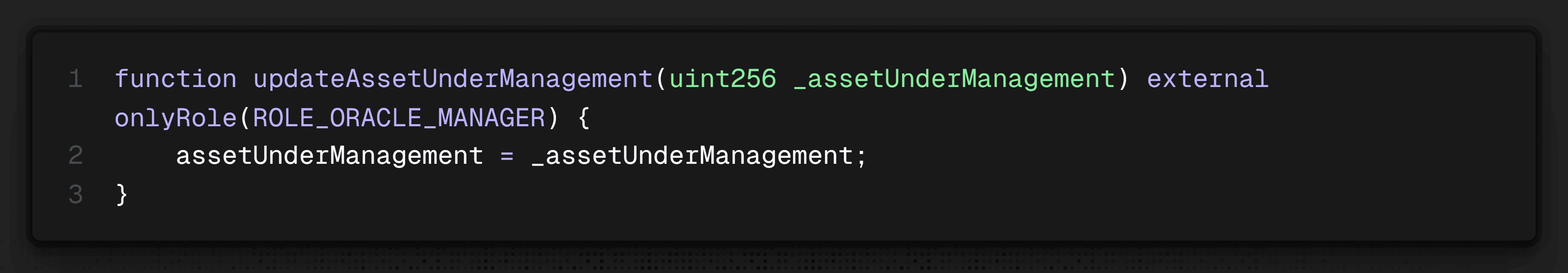
This is efficient and cheap. But it also creates a critical vulnerability:
Any compromised Oracle key can arbitrarily change AUM
This can distort pricing
Enable over-minting or unfair withdrawals
Or trigger cascading economic exploits
This is exactly the class of failure seen in many hybrid systems.
cSigma’s Approach: Designing for Worst-Case Scenarios
At cSigma, we assume that any privileged role can fail. Instead of trusting inputs blindly, we enforce defensive constraints at the contract level.
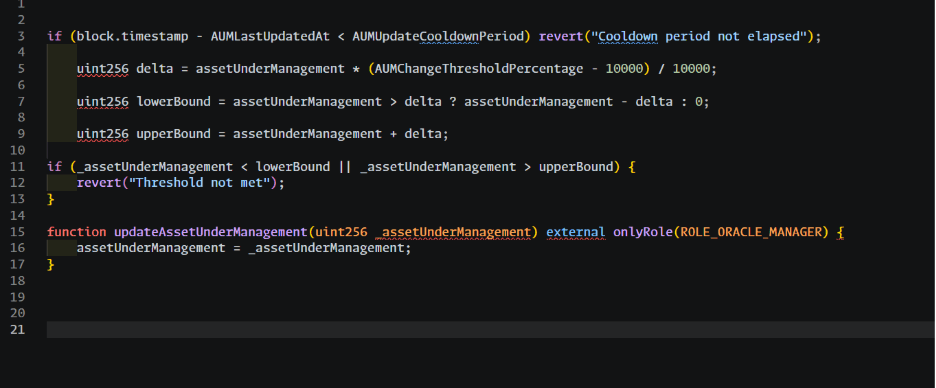
Below is the actual pattern used:
Key Safeguards Implemented
Here are some of the key safeguards implemented:
1. Threshold-Based Validation
AUM updates must fall within a predefined range relative to the previous value.
This prevents:
Sudden spikes or drops
Arbitrary manipulation
Large-scale minting exploits
Even if a key is compromised, the attacker cannot push extreme values.
2. Cooldown Mechanism
Updates are rate-limited:
This ensures:
Updates cannot be spammed
Attack velocity is reduced
The team has time to detect and respond
3. Bounded State Transitions
Instead of allowing unrestricted state changes, the system enforces bounded transitions over time.
This transforms:
Instant catastrophic failures into gradual deviation that can be detected and stopped
4. Time as a Security Primitive
By combining thresholds and cooldowns, cSigma effectively introduces time-based protection:
Attackers cannot execute large changes instantly
Exploits become slower and more visible
Emergency response becomes possible
Security Comes at a Cost - And That’s Intentional
These safeguards increase:
Gas cost
Operational overhead
Complexity
We could have optimized for efficiency. But we chose not to, because: Security and robustness always come with a cost.
In RWA systems-where assets represent real-world value—this tradeoff is not optional.
Design Principle: Assume Failure, Not Perfection
One of the biggest mistakes in DeFi system design is assuming:
Keys will remain secure
Infrastructure will not fail
Off-chain components will behave correctly
History shows otherwise. The AWS KMS exploit is not an isolated case-it is a pattern. Systems fail not because code breaks, but because assumptions break.
Conclusion
As DeFi expands into real-world assets, off-chain inputs are unavoidable. But they must never be blindly trusted.
Secure protocol design requires validating every external input, limiting the impact of compromised roles, and designing from scratchkeeping failure in mind.
Validating every external input
Limiting the impact of compromised roles
Designing for failure, not ideal conditions
At cSigma, this philosophy is embedded directly into smart contracts.
Because in financial systems, The difference between a secure protocol and a vulnerable one is not trust-it is control.